CCleaner is a small program design to optimize your Windows operating system. Read More
Month: March 2011
CCleaner 3.04.1389
CCleaner is the number-one tool for cleaning your Windows PC. It protects your privacy online and makes your computer faster and more secure. Easy to use and a small, fast download. Read More
How can I open PowerPoint presentations without having Office installed
One of the most common format of electronic presentations is the .ppt (Microsoft Power Point).
As you may know .pps files can be open with Power Point software from the Microsoft Office suite. Microsoft Office is a suite of software that is not free. Therefor, if you only need to view this presentation files you have to know that Microsoft offers you a free option: Read More
What’s the difference between spyware, malware, adware, trojan horses …?
 A virus (computer virus) is a piece of software that is designed to intentionally cause damage to a computer. It has the ability to copy itself and infect different files and computers. Depending on the mode of operation, we can define several types of viruses:
A virus (computer virus) is a piece of software that is designed to intentionally cause damage to a computer. It has the ability to copy itself and infect different files and computers. Depending on the mode of operation, we can define several types of viruses:
- Spywares are the programs that collects small pieces of information about users without their knowledge. They are intended to monitor/Log the activity performed on a computer. These are used to spy on some one either for legal or illegal perpose.
- Keyloggers (use Keystroke logging) are examples of spywares. This type of software track (or log) the keys struck on a keyboard, typically in a covert manner so that the person using the keyboard is unaware that their actions are being monitored.
- Malwares or malicious software are programs with malicious intention. This term defines all the unwanted and malicius software installed in a computer (viruses if you want). This software can damage your computer, spy on you or perform any other malicious task.
- Adwares are unwanted programs that automatically plays, displays, or downloads advertisements to a computer (generally in POP-UP’s form). They are not intended to harm your computer. The object of the Adware is to generate revenue for its author.
- Trojan Horse is a program which is used to gain access to a computer. It’s main function is to open doors for unwanted external access. Trojans are also known as Backdoors. They may allow a hacker to remote access to a target computer system.
- Worm are known in the context of computer networks. They are programs that self- replicate and uses a computer network to send copies of itself to other computers and it may do so without any user intervention. They often slow down the network.
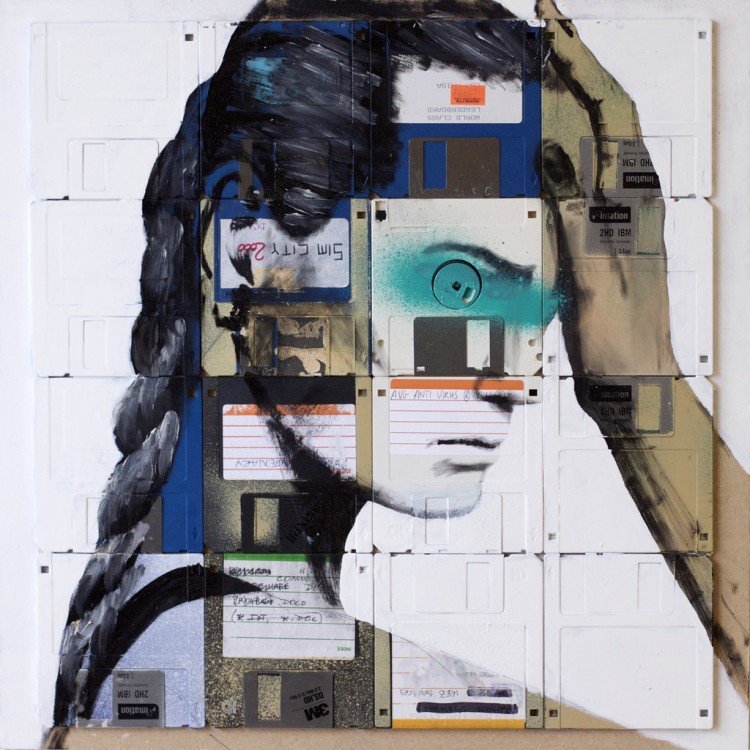
Photo: [Nick]
Which combination of keys are used to create a heart symbol?
To add symbols you should use a combination of two keys : ALT + “NUMBER”
where “NUMBER” is a key (number) from your numeric keypad.
For example, if you want to insert a heart symbol you should: Read More